
PEO EIS’ Defensive Cyber Operations office is achieving rapid acquisition of constantly evolving IT by using consortium-based other transaction authority.
by Lt. Col. Scott Helmore and Tom Cole, Brig. Gen., USA (Ret.)
How to acquire and provide capability better, faster and cheaper has been a consistent theme in defense acquisition for decades. In this era of cyber, information technology (IT) and software-intensive systems, technology moves faster than the traditional acquisition system can support. Traditional timelines for requirements, funding, development, production and fielding span years. By the time systems are delivered to Soldiers, the need they were designed to fill may be several years old.
This problem has confounded Army leadership, which demands a more expedited acquisition system that can measure success in months or less. One example of a more expedited acquisition approach is underway in Defensive Cyber Operations (DCO), part of the Program Executive Office for Enterprise Information Systems (PEO EIS). DCO is implementing an acquisition strategy that incorporates the use of consortium-based other transaction authority (OTA) to inform requirements. The result is to deliver early capabilities with the acquisition efficiency necessary to provide a suite of defensive cyber capabilities in a relatively short amount of time.
In December 2016, the Army acquisition executive formed Product Manager DCO within PEO EIS, designating it as the office responsible for nontactical materiel solutions to counter cyber threats. DCO is a capability provider for the Army’s cyber protection brigades, teams and other cyber mission forces operating in a complex multidomain battlespace. The immediate challenge facing DCO is how to provide effective and relevant tools in a timely manner.
The concept of operations for defensive cyber is complex, with capabilities dispersed across the battlespace and continually adapting to an evolving threat. To accommodate this environment, DCO capabilities and requirements need to address passive and active threats as well as multidomain integration. They need to focus on protecting data, networks and net-centric operations. Finally, they must be interoperable with other IT and software-dependent systems.
The proper identification of DCO requirements and their operational interrelationships is difficult to conceptualize and can be extremely labor intensive. To help overcome this challenge, DCO recognized that rapid prototyping, with early and continuous collaboration with industry, is essential to effective delivery of cyber capabilities. DCO is using the Consortium for Command, Control and Communications in Cyberspace (C5), established in September 2011 by Army Contracting Command – New Jersey, to enable this collaborative prototyping model to provide innovative solutions quickly to the Soldier. The C5 OTA provides government offices with the necessary problem-solving environment, leveraging nontraditional defense contractors, small businesses and more traditional defense partners.

Product Manager DCO’s mission is to provide essential capabilities to Army cyber protection teams in a streamlined, efficient and integrated approach. Each system in the DCO family of 11 systems can operate autonomously or be combined into an integrated capability. (Graphics by Product Manager DCO)
WHAT’S THE DIFFERENCE?
DCO is focused on providing capabilities to address the 2016 Joint Staff-approved DCO Information Systems Initial Capabilities Document (ICD). This ICD uses the Joint Capabilities Integration and Development System IT Box method, an adaptable and flexible requirements approach that provides rapid capabilities to the Soldier through use of a further delegated requirements process. Under the IT Box, services are delegated the approval for all derived requirements within the limits of specified cost and scope thresholds. The IT Box establishes the overarching authority to create the DCO family of systems (currently, there are 11).
The 11 systems comprise six initial programs of record, all expected to be Acquisition Category III, with an additional five programs identified for future development. The initial six capabilities focus on giving cyber protection teams platforms that provide remote access to key terrain in cyberspace. These platforms are either embedded at vital garrison locations or in tactical formations, or used as flyaway systems (that is, transportable on commercial airlines) that give the teams a foothold from which to unleash their other capabilities—cyber protection team tools, mission planning capability.
In addition to these platforms, the initial DCO capabilities provide the early warning or reconnaissance capability via the Army’s Big Data Platform. This platform monitors cyber data, performs analysis and provides cyber defenders with an aggregation capability that is always looking for the unknown. To perform missions, whether on-site or remotely, cyber defenders need effects (the ability to deny, degrade, disrupt, destroy and manipulate), which are provided through a variety of commercial, open source and government-owned tools. Finally, a mission planning platform—currently based on the Defense Advanced Research Projects Agency’s Plan X project—enables users to visualize, plan, command and manage the force.
Combining all of these capabilities gives the cyber protection teams an integrated DCO capability, in the same way that combining Stinger missiles, a High Mobility Multipurpose Wheeled Vehicle, a Sentinel radar, and forward area air defense command, control, communications and intelligence provides air defense units with short-range air defense capabilities. Each system can operate autonomously or be combined into a mutually supportive integrated capability.
To meet the flexibility of the IT Box method, Product Manager DCO has recognized that traditional acquisition processes focusing on the refinement of requirements and risk-reduction prototyping through a balance of Joint Capabilities Integration and Development System (JCIDS) documentation and milestone decisions, contracting and documentation tasks would simply not be responsive enough. Adversaries develop new threats like the WannaCry Ransomware, Zeus Trojan, or Petya malware and exploit U.S. systems weekly; cyber defense technologies emerge just as quickly.
DCO designed an evolving acquisition strategy with continual prototyping to test technologies, inform requirements, deliver capabilities and allow rapid technology insertion, thereby staying ahead of the ever-evolving threat. A correspondingly flexible acquisition vehicle is essential to allow for innovative technology to be incorporated into evolving capability enhancements. DCO capabilities are less focused on the engineered solution than on solution modularity―how easy is it to adapt, interface or replace.

The C5 process starts with the government user providing the C5 consortium with a concise statement of needs. C5 members are notified by the Consortium Management Group, a nonprofit that administers the consortium. Members propose solutions. Army Contracting Command reviews the proposed solutions and can combine multiple ideas. The awardee, and any subcontractos, then build the government a proof-of-concept prototype and potentially continue with follow-on production. (Graphics by Product Manager DCO)
INSIDE OTA
Additionally, DCO requires a strategy that fosters continual industry collaboration and innovation to take full advantage of the problem-solving and development of effective solutions through prototyping enabled by C5 and OTA. Leveraging the skills of a consortium of experts to combine solutions into an integrated, potentially game-changing capability offers a higher potential for success than depending on a single solution provider.
The consortium-based OTA construct allows government participants to collaborate with innovative industry experts and then award an agreement to build a prototype that demonstrates solutions to problems. This strategy capitalizes on acquiring innovative cyber, IT and software-intensive capabilities comparatively quickly—a model that DCO plans to use to address evolving threats and technologies.
OTAs are not new, although most acquisition professionals have not used them. They have existed since 1958, under authority initially granted by Congress to NASA to support development of space exploration technologies with a responsive approach. Over the years, through separate and specific statutes, 11 federal departments and agencies have added OTAs to their models, including the Departments of Defense, Energy, Health and Human Services, Homeland Security and Transportation.
Recently, Congress amended and further expanded DOD’s OTA/ Section 815 of the National Defense Authorization Act for Fiscal Year 2016, 10 U.S.C. §2371b, adding the ability for the government to easily transition a successful OTA prototype project directly to a follow-on production contract when the initial prototype effort is competitively awarded.
The consortium-based OTA is in itself a competitive environment. C5 is operated by a nonprofit company, Consortium Management Group (CMG), created to establish, operate and manage consortia formed under the National Cooperative Research and Production Act to use OTA. This Section 815 OTA provides the legal framework and contractual means for C5 industry members to collaborate with government customers and other members and subcontractors to provide innovative solutions for DOD. With over 400 industry representatives and established processes, C5 presents DCO with the perfect balance of a collaborative environment, access to emerging technology providers, access to nontraditional DOD innovation and the potential to team with traditional DOD industry expertise.
The consortia are designed to have broad technical focus areas to accommodate many different types of prototyping efforts. The C5 process starts when the government user, such as an Army program manager (DCO, for example) provides the C5 Government Acquisition Liaison Office at Picatinny Arsenal, New Jersey, with a concise statement of needs. (See Figure 2.) CMG notifies the C5 consortium members of a particular need in a request for white papers; those that believe they have a good approach propose solutions. The government reviews the industry white papers and may combine multiple ideas into a best-of-breed solution for a prototype.
This is unlike the traditional process, based on the Federal Acquisition Regulation, whereby the government generally must either select the contractor that is closest to its requirement, or reject all proposals and restate the requirement—a time-consuming, “good enough” method. With the C5 OTA, the government collaborates with industry to put together a solution and optimizes innovation. Once they’ve agreed on the solution, they document their approach in an OTA. The entire process, which generally takes about 90 days, allows the awardee to build the government a proof-of-concept prototype and potentially continue with a follow-on production.

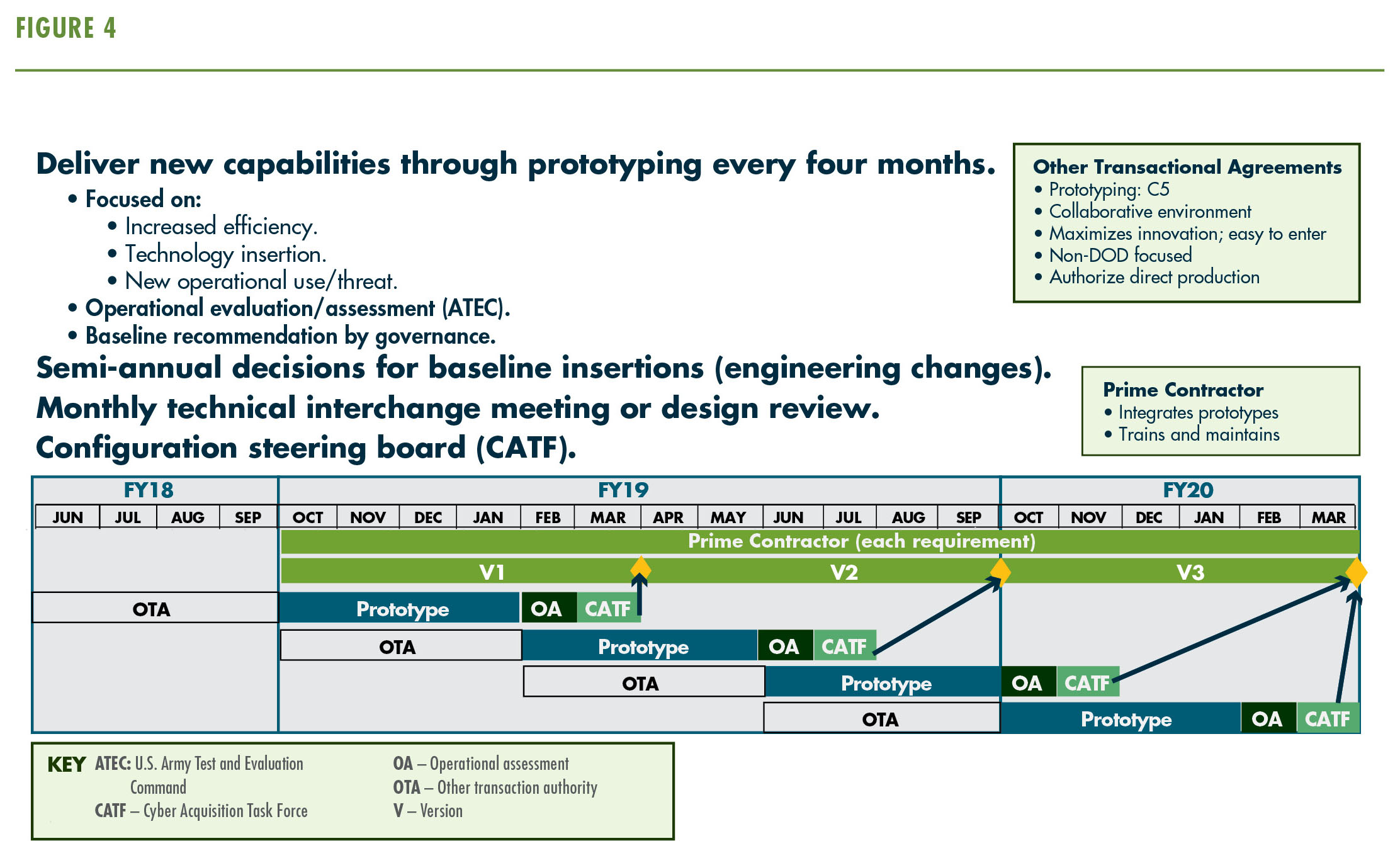
DCO delivers evolving capabilities—technology enhancements, improved efficiency or new specific-use capabilities—every three to four months. The evolving capabilities are then assessed, refined and integrated into the baseline capability. (Graphics by Product Manager DCO)
ANATOMY OF AN ACQUISITION
The DCO acquisition strategy takes advantage of flexibility in requirements and contracting methods to adopt practices from rapid software and hardware development. DCO is delivering capabilities as an evolving “build” or “drop” every three to four months—not necessarily the complete solution but rather technology enhancements, improved efficiency or new specific-use capabilities that are assessed, refined and then integrated into the baseline capability. (See Figure 3.)
By using the C5 OTA, the product office can build continuous prototypes to assess capability gaps and insert mature technologies into the baseline program. (See Figure 4.) At the same time, the OTA prototyping strategy informs the U.S. Army Training and Doctrine Command capabilities manager and provides the basis to discuss requirements, potentially refining key performance parameters by adjusting capability drop documentation under the IT Box construct. The end result is the most advanced capability that industry can provide, properly aligned with program requirements integrating attributes of doctrine, organization, training, materiel, leadership and education, personnel and facilities in a rapidly moving acquisition scenario.
DCO expects that using C5 and incorporating OTA prototyping will result in acquisition of a capability that is:
- Better—Continuous prototyping will allow DCO to provide capabilities that respond to evolving needs and align properly with requirements.
- Faster—Timelines are at least 50 percent shorter, compared with traditional acquisition methods.
- Cheaper—Effective prototyping reduces a product’s life cycle costs by providing a tangible solution that can integrate with existing systems and be tested up front for long-term suitability before full production decisions and the associated expenses.
PM DCO, under a C5 OTA, builds continuous prototypes to assess capability gaps. (Graphics by Product Manager DCO)
CONCLUSION
In this era of expanding cyber technologies and threats, as well as IT capabilities, traditional acquisition methods and approaches generally deliver obsolete capabilities too late and over budget. Through more innovative approaches, such as use of the JCIDS IT Box requirements process and consortium-based OTA, acquisition can move closer to the goal line of a better, faster, cheaper solution that harnesses the continual emergence of new technologies and the risk reduction capabilities of prototyping.
There is no more urgent time than today, as we fight ongoing cyber battles in industry and government, for acquisition professionals to improve their use of innovative tools, such as OTAs, and maximize collaboration with industry. Through use of the C5, monthly technical interchange meetings and rapid prototyping, DCO intends to demonstrate the might of combined industry solutions and collaborative acquisition to provide the most responsive capabilities possible.
For more information on DCO, go to http://www.eis.army.mil/programs/dco. For more information on C5, go to https://c5technologies.org.
COL. SCOTT HELMORE is the product manager for the Army’s Defensive Cyber Operations office under PEO EIS. He holds an M.S. in acquisition systems management from the University of Management and Technology and a B.S. in agricultural business from Michigan State University. He is Level III certified in program management.
TOM COLE, BRIG. GEN., USA (RET.) currently serves as an independent consultant. He completed over 30 years of active Army service, with 22 years in defense acquisition. He was the program executive officer for Intelligence, Electronic Warfare and Sensors from November 2007 to September 2010. A graduate of the U.S. Military Academy at West Point, he holds an M.S. in aerospace engineering from San Diego State University and an M.S. in national resource strategy from the National Defense University’s Industrial College of the Armed Forces.
This article will be published in the January – March 2018 issue of Army AL&T Magazine.
Subscribe to Army AL&T News, the premier online news source for the Acquisition, Logistics, and Technology (AL&T) Workforce.

