
CYBER DEFENSE: Representatives of civilian companies and military leaders attend Cyber Shield 19 at Camp Atterbury, Indiana, in April 2019. Cyber Shield is the premiere unclassified defensive cyberspace operations exercise for collective training and technical assessment with industry partners. (Photo by Spc. Joshua Syberg, 120th Public Affairs Detachment)
Cyber threats require a lightning-fast response. With innovation at the heart of its organizational culture, Applied Cyber Technologies designed an acquisition formula for speed.
by Fianna Litvok
Change rarely comes easily to large organizations, and it is especially difficult for organizations that are steeped in standardization, formulaic procedures and repeatable methods. Culture change, in particular, is infinitely more challenging than changes in processes or policies.
The DOD acquisition workforce is undergoing a fundamental shift in cultural mindset. After years of employing encumbered, linear acquisition processes, DOD is moving toward agile acquisition. This change comes out of necessity—our current threat landscape demands a framework that allows for more flexibility and less rigidity. While these changes are welcome, it is reasonable to assume that it will take a while for the new mindset to become ingrained and for DOD’s acquisition culture to truly change. There is plenty of reason to be hopeful, however, thanks to the early efforts of forward-thinking program offices and the subsequent emergence of updated acquisition policies and the Adaptive Acquisition Framework.

DEFENSIVE EXERCISE: Nearly 600 Soldiers from more than 40 states participated in the National Guard’s Cyber Shield 20 exercise Sept. 12–27. The defensively focused tactical annual cyber exercise was hosted virtually this year and gave Idaho Soldiers the chance to develop and use their cyber defense skills while building key relationships with the state’s Office of Information Technology Services, its mission partner. (Photo by Master Sgt. Becky Vanshur, Idaho Army National Guard)
DEFENSIVE CYBER’S NEED FOR SPEED
At Applied Cyber Technologies (ACT), a program within the Defensive Cyber Operations (DCO) portfolio of the Program Executive Office for Enterprise Information Systems (PEO EIS), flexibility is part of the organization’s DNA. ACT is charged with defining ways to rapidly assess, integrate, acquire, field and maintain advanced defensive cyber solutions for the Army’s cyber defenders. When ACT was stood up in 2018, there was no precedent to follow, and many questions had yet to be answered. In the absence of an established operational framework to follow, ACT stepped into uncharted waters and expected to make some waves.
Since its inception, ACT has looked for ways to produce and field the most innovative solutions to cyber defenders as quickly as possible. In many ways, this required looking at the problem through an entirely new lens. ACT realized that in order to increase speed, it needed to close the gap between solutions development and delivery, and system fielding and feedback. Just as critical to the equation was implementing industry-tested agile methodologies and maximizing relationships with industry partners. By zeroing in on the problem that needed to be solved and identifying the best practices to address the problem, ACT developed the ability to work at speeds never before realized.

BIG DATA: Lt. Col. Peter Amara, product lead for Applied Cyber Technologies (ACT), briefs Jeffrey White, then the principal deputy assistant secretary of the Army for acquisition, logistics and technology, on the Army’s Big Data Platform. (Photo by Jennifer Sevier, Defensive Cyber Operations)
CRUNCHING THE NUMBERS
Within 18 months of opening its doors, ACT created a framework for rapid acquisition, developed a robust vendor ecosystem and created a collaboration workspace that became the Army’s innovation center for defensive cyber prototypes. In 2019 alone, ACT awarded 12 software tool prototypes at a cost of $12.8 million, with an average lead time to award of four to six months. Additionally, ACT hosted 3,500 visitors and held more than 250 events, including cyber exercises for the U.S. Army, Air Force and Marine Corps.
More recently, ACT developed its Defensive Cyber Operations Resource for Updates, Innovation and Development (DRUID), a cloud-based continuous integration and continuous delivery pipeline that reduces systems integration time for tools from months to approximately one week. ACT developed DRUID in order to push systems integration to the beginning of the acquisition process, thus allowing for better informed—and much quicker—prototype project award decisions. Since these decisions can now happen much earlier in the process, the overall time to acquire tools is greatly reduced. Additionally, DRUID enables ACT to receive an increased number of tools for assessment, allowing it to evaluate more tools in a much shorter period of time. Interestingly, one of the most innovative features of DRUID is its ability to shift the cost of tool integration from government to industry. ACT understood that industry would willingly offer prototypes at no cost in exchange for the chance to secure an award.
During summer 2019, in the first other-transaction authority (OTA) prototype round using DRUID, 22 vendors successfully delivered functional tool images containing prototypes through the pipeline. It took less than one week, and the only cost to the government was the outlay for DRUID, which is a mere fraction of what it would have cost to get the 22 tool images ACT secured in just the first OTA prototype round.
DRUID greatly expands the breadth of vendor participation, significantly reduces tool integration time, increases the number of tools that can be assessed and eliminates the government’s upfront cost for prototypes. This approach will enable ACT to provide the most effective solutions to cyber defenders quickly, while saving the government a significant amount of money in the near and long term.

FIELD TRAINING: Capt. Richard Shmel, a cyberspace operations officer, participates in the 915th Cyber Warfare Battalion’s Field Training Exercise in October at Muscatatuck Urban Training, Indiana. (Photo by Steven Stover, 780th Military Intelligence Brigade (Cyber))
Of course, advances like DRUID never happen in a vacuum. ACT’s team and industry partners were critical to making it all happen. But, more than anything, ACT’s culture has been its strength. ACT is fortunate to have developed a culture that inspires its team to think outside the box, to look at things a bit differently and to take chances.
“ACT provides a place for the brightest minds in cyber to collaborate, exchange ideas freely and develop the next generation of cyber solutions,” said Lt. Col. Peter Amara, product lead for Applied Cyber Technologies. “In order for a game-changing innovation like DRUID to flourish, we had to remove the prescriptive processes and rigid restrictions that have stifled technological creativity. I’m proud of our team and what we’ve accomplished so far, from both a technology innovation and acquisition perspective, but I believe the best is yet to come.”
CONCLUSION
Out of sheer necessity, ACT developed a way to do rapid acquisition by embracing a culture of change and innovation. Now, with the publication of updated DOD guidance and the Adaptive Acquisition Framework, the acquisition workforce has a promising way forward. Understandably, culture change is never easy and takes time. Some programs will lead the way; others will make changes slowly and perhaps somewhat reluctantly. However, change for the better is always worth making, even if it is uncomfortable at the time. Agile acquisition processes enable program managers to provide the best possible capabilities as quickly as possible to Soldiers, and in the end, they are the reason for all this.
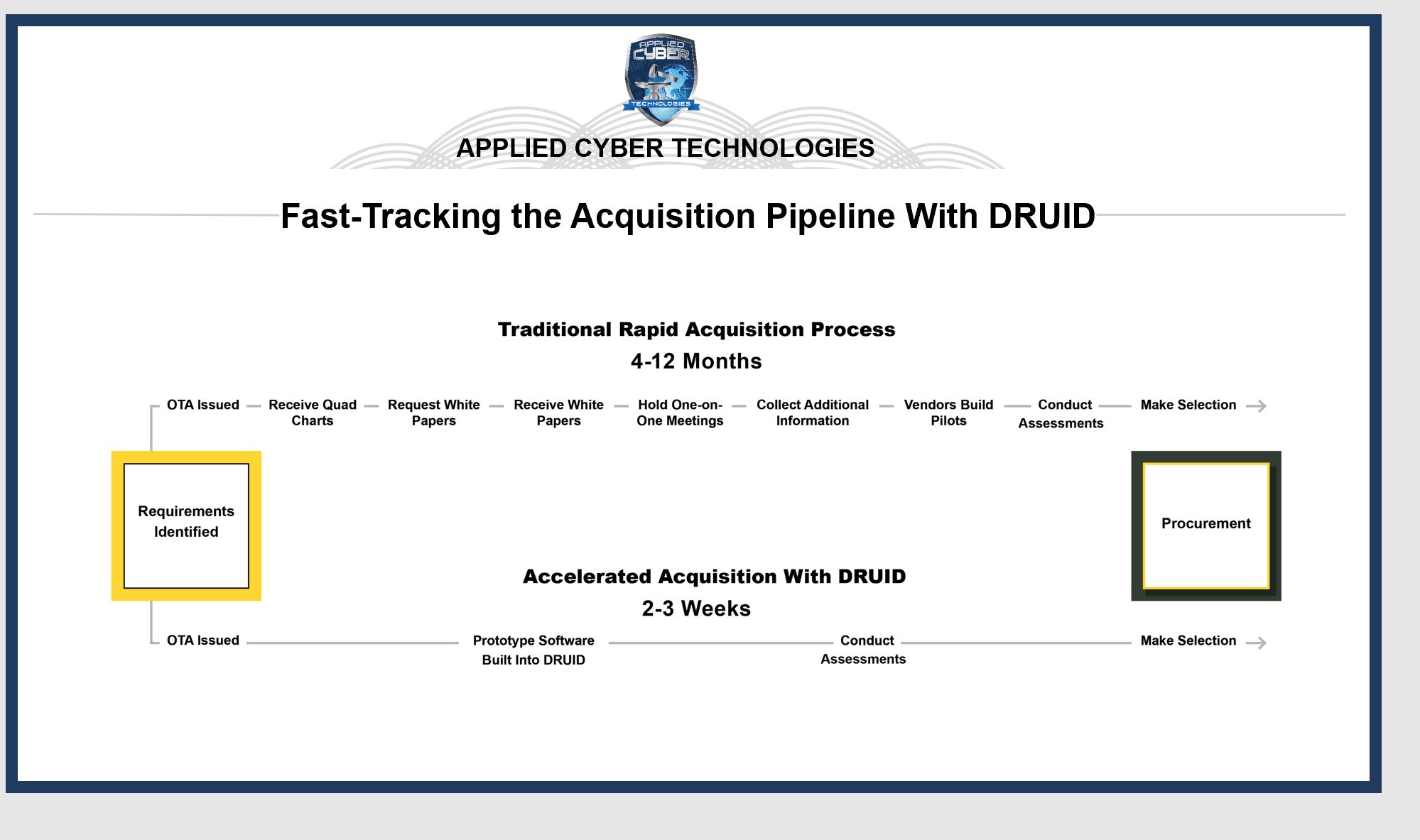
DRUID PIPELINE: Applied Cyber Technologies’ (ACT) agile DRUID pipeline significantly streamlines the technology acquisition process. (Graphic by Katherine Lindsey, ACT)
For more information, visit https://www.eis.army.mil/programs/act.
FIANNA LITVOK is the communications lead for Applied Cyber Technologies. She also serves as a military intelligence chief warrant officer in the U.S. Army National Guard’s 91st Cyber Brigade. She holds an M.A. in English and B.A. degrees in English and history from Stony Brook University. She is certified in Scalable Agile Frameworks for Program Owners/Program Managers and Information Technology Infrastructure Library.
Read the full article in the Spring 2021 issue of Army AL&T magazine.
Subscribe to Army AL&T – the premier source of Army acquisition news and information.
![]()

