
VIRTUAL SOLUTIONS: Team No Sim, No Train—Ksenia Kerentseva, Vipin Verma and James Cook—from Arizona State University works with Airmen at Davis-Monthan Air Force Base in Tucson to improve training for maintenance personnel of the 355th Maintenance Group using virtual reality training software. (Photo by James Cook)
Defense innovation class started at Stanford has now spread to 47 universities.
by Michael Bold
Pete Newell knew something was up when he looked around the Stanford University classroom being used for the first-ever Hacking for Defense class.
“When we taught the first class at Stanford we opened the door for anybody who wanted to come,” Newell, a retired Army colonel who spent the last several years of his career as director of the Army’s Rapid Equipping Force, told Army AL&T in an April interview. “We had 32 students, two teaching assistants and four instructors. So there were 38 of us. The room sat 90 people and it was standing room only.”
Stanford professors, venture capitalists, representatives from other universities, government experts and others had driven in from around Silicon Valley and had flown in from all over the country to witness the class, which unleashed teams of students on unclassified, real-world problems from DOD.
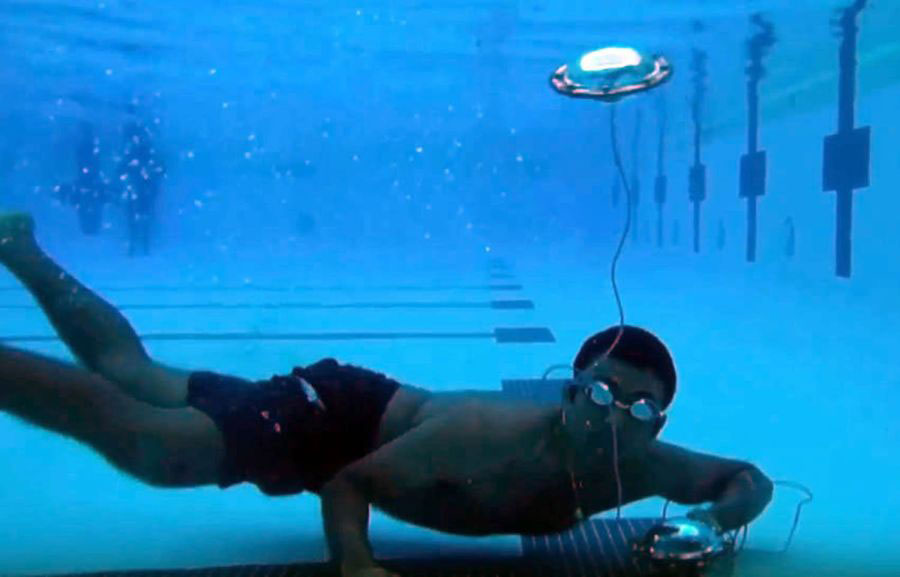
TEST EARLY: A member of Team AquaLink conducts an underwater test on an experimental GPS buoy as part of the Hacking for Defense course at Stanford University. (Photo by Team AquaLink)
A lot has happened since that first Hacking for Defense class on April 4, 2016. The movement started by Newell, CEO of BMNT Inc., a company that pairs Silicon Valley technical wizardry with defense and intelligence agencies; Steve Blank, a retired Silicon Valley “serial entrepreneur;” and Joe Felter, a retired Army Special Forces colonel and founder of BMNT; assisted by Dr. Tom Byers, entrepreneurship professor at the Stanford School of Engineering, has since exploded:
- The course is currently being taught at 47 universities nationwide, including the U.S. Military Academy at West Point, the U.S. Air Force Academy, Defense Acquisition University and the Naval Postgraduate School.
- Hacking for Defense is a DOD program of record, funded by Congress.
- More than 2,000 students have completed the program, addressing more than 750 national security problems.
- It has directly led to the formation of 14 startups, including the satellite company Capella Space; the mobile training platform Learn to Win, which is changing how fighter pilots are trained; Anthro Energy, which developed a flexible nonflammable lithium ion battery being used by wearable electronics makers in straps or wristbands (and whose CEO was named to the Forbes 30 under 30); and Lumineye, which developed a device that helps first responders see through walls and which was the grand prize winner of xTechSearch 2.0, sponsored by the Office of the Assistant Secretary of the Army for Acquisition, Logistics and Technology.
- It’s spawned a series of sister programs, including Hacking for Diplomacy, Hacking for Local, Hacking for Oceans and Hacking for Homeland Security, among others. In the United Kingdom, Hacking for MOD (Ministry of Defense) is being taught at seven universities. In Australia, Hacking for National Security being piloted at the University of New South Wales.
BIG HILL TO CLIMB
Newell had gone into the class just hoping they could attract enough students. “We thought we were just gonna teach a class at Stanford,” he said. They had to convince sponsors, the university, students and mentors that their class would be worth their time and effort. And then there was the government. One issue was whether “we could convince the government to not just give up problems, but also participate in the class,” Newell said in describing the challenges. “The second one was that we could convince Stanford to let us teach the class. And … that we’re going to attract enough students to make it interesting. And at the same time build the network around them, which means we had to recruit mentors and we had to recruit advisers. So our expectation was that we would pull off a moderately successful class and that it would be something we repeated once a year.”
But Blank, ever the entrepreneur, had visions of much more. Blank’s Lean LaunchPad had revolutionized the way startups set up shop in Silicon Valley and had landed him on the cover of the Harvard Business Review. “On day one, my thinking was there’s no sense creating a new class if you’re not going to try to make it a national program,” Blank said in an April interview. “That was my idea from the get-go.”
His Lean LaunchPad method boiled down to three basic steps:
- Articulate your hypotheses: What problem are you trying to solve? Who’s your customer? What solution do customers want to grab out of your hands?
- Get out of the building. Talk to at least 100 potential customers and stakeholders about your hypotheses. Have you identified the problem correctly? Can you validate your hypotheses?
- Build a minimum viable product (MVP)—the smallest thing that will get you the most learning at that point in time. It can be a wireframe, a PowerPoint, hardware, etc. Get customer feedback. If the feedback is good, refine and improve your MVP until it’s ready to roll out as a finished product. If it’s bad, figure out where you went wrong and then pivot. This way, if you’ve failed, you’ve failed early and inexpensively.
Blank had expertise turning his Lean LaunchPad methodology into a successful classroom experience. In 2011, he was asked by the National Science Foundation to find a way for its scientists to turn their research into viable commercial products. He developed the Innovation Corps (I-Corps), which is now considered the standard for science commercialization in the U.S. and has been adopted by other government agencies including the National Institutes of Health. I-Corps teams have created more than 1,100 startup businesses.
“I realized I already had a class, so we didn’t have to create one from scratch,” Blank said. The difference was that in I-Corps the students brought their own problems to work on. In Hacking for Defense, DOD and the intelligence community would need to supply a list of problems that teams of students would pick from. So that was one challenge. What’s more, Blank was worried about how the class would be received at Stanford, where in the 1960s violent anti-Vietnam War protests forced the university to end all classified research.
“So that was kind of my worry, that we would throw a party and no guests would show up, or we’d throw a party and the guests would show up but not the caterer,” he said.
Everyone ended up making the party, and then some. As Hacking for Defense developed and spread to other universities, several truths began to emerge. Among then, Blank said, “is that you could quickly immerse non-military folks deeply into problem understanding, and then have them rapidly test different solutions. At the same time taking the sponsor for the ride, because almost always what we’ve discovered is the problem that is given is almost always a symptom of some other problem.”
“We thought we would teach the government how to better deliver problems and create a dialogue that was worthwhile,” Newell said. “We thought that the entrepreneurship component of the course would get students excited about, you know, this is how you wanted to build a company. This is real world and it’s real experience working with real people.”
Buy-in from the government side—and at a high level—was critical. “If there’s a challenge in scaling the course it has been retaining the discipline around the problems,” said Newell. “There has to be a real problem, there has to be the problem owner and there has to be somebody who’s energized and passionate about solving the problem. There has to be a senior leader champion that has the resources and the authority to do something about it. It has to be important to the organization that is vested in the work being done by the class.”

IMMERSIVE EXPERIENCES: Members of Team 21st Century Frogman—from left, Andrew Sparks, Gerardo Rendon, Kelsey Schroeder and Priyanka Sekhar—took part in some aspects of Navy SEAL Basic Underwater Demolition training at Naval Amphibious Base Coronado, California, during their Hacking for Defense class at Stanford in spring 2017. Their problem was to create an algorithm and dashboard to predict safety risks and streamline real-time data entry during SEAL basic training. (Photo by Team 21st Century Frogman)
LIFE CHANGINGFor many of the students it’s been a life-changing experience. Max Weintraub was a member of Team Spyglass at Georgetown University’s Hacking for Defense class in January 2017. Its mission was to help the Army Asymmetric Warfare Group find actionable intelligence from large amounts of social media data in order to identify immediate, localized threats to forces on the ground.
After getting his bachelor’s degree at the University of Arizona in creative writing and Italian, Weintraub went to graduate school at Georgetown to get an MBA and was looking to pivot into technology. “At first I was kind of skeptical as to why the class even existed,” he said in an interview. “I had no real background in working with the military, so I was kind of confused as to why the military wanted a team of Georgetown students, none of whom had any military experience, to help solve a problem. I assumed that there was an easy button behind the scenes that the military could click anytime there was a problem. … It became pretty clear early on that that was not the case. In fact, many of the types of problems that the military faces are things that, in essence, have been solved in the commercial sector, but for various reasons there’s not an effective analog for the military. What they were really looking for was creative thinking from outside of the box to try to come up with novel concepts that could help them solve the problems that they were facing.”
A lack of military knowledge on the part Weintraub’s Team Spyglass didn’t stop them from coming up with solutions. “I went from not knowing the difference between a company and a battalion to briefing Gen. [Paul M.] Nakasone at Cyber Command on the ideas that we developed over the course of a single semester.
“What it triggered for me was realizing that I have a passion for problem solving,” he said. Weintraub now works as a program manager at the National Security Innovation Network, a DOD program under the Defense Innovation Unit that seeks to bring together defense, academic and entrepreneurial innovators to solve national security problems.

GET OUT OF THE CLASSROOM: Members of Team Spyglass—from left, Jose Gabriel Andrade, Katerina Sedova, Chloe Krawczyk and Max Weintraub—got hands-on M4 training at a shooting range at Fort Meade, Maryland, while working with members of the Asymmetric Warfare Group. (Photo courtesy of Katerina Sedova)
TEACHING IN A PANDEMIC
As with everything else, the COVID-19 pandemic threw a monkey wrench into how Hacking for Defense was taught. “We were really concerned because our class is really built on getting students out of the classroom and talking to real people,” said Newell.
There were positive and negatives from the restrictions brought on by quarantine and the move to virtual learning, Blank said. “It turned out that there was good news and bad news. The good news is you could do interviews even easier, and get to more people, higher-ranking people, without gatekeepers, via Zoom,” he said. “And so access to people you needed to talk to was actually two to three times easier for students.” The bad news was that students couldn’t immerse themselves into the community they were trying to solve problems for. No becoming a qualified diver, no taking part of a Navy SEAL basic training course, no chance to don and move around in an explosive ordnance disposal suit, all of which have been part of various H4D classes. “And so students lost that,” Blank said.
NATIONAL PUBLIC SERVICE
One of the primary motivations at the start of Hacking for Defense was finding a way for students to serve their country in a nontraditional way. The idea of national public service has struck a chord both with students and universities.
“I’m not going to serve in the armed forces,” Luke Truitt, a Hacking for Defense student at Duke University, said in a video produced by Duke on the H4D program. “Is there some way I can help? And I feel like this is one good step in that direction.”
Universities were also interested in finding a way for students to serve the greater good. “Educators involved in teaching entrepreneurship … kind of self-formed into a group of folks who were interested in using entrepreneurship as a platform for national public service,” Newell said.
BMNT’s nonprofit arm, the Common Mission Project, which runs the Hacking for Defense program, began a quarterly meeting with entrepreneurs, professors and university leaders from around the world to discuss not only how to best teach entrepreneurship, but also to share ideas about promoting entrepreneurship for social good, Newell said. “The first time we ran one I think we had about 90 educators from around the country. The last one we did was about two months ago, we had over 600 educators from 65 different countries join us.” The next meeting, in June, will focus on how to build back better after COVID, how to accelerate recovery and how to build more resilience into the economy. “All from the concept of building an H4D program at Stanford,” Newell said.
“My motivation for Hacking for Defense was not only just the class, but for national service,” Blank said. Ending the military draft in the 1970s and not replacing it with some sort of national service was a mistake, Blank believes. “We bought into a 40- to 50-year science experiment that says, ‘What happens when you disconnect your population from having skin in the game?’ It has not been a good outcome for the country. When there’s no national unifying place where people of different cultures and different backgrounds and opinions get to physically mix, instead you get these narrow silos or virtual ones like Facebook, and they don’t end up well.”
For more information, contact the author at mbold@networkrunners.com.
MICHAEL BOLD provides contract support to the U.S. Army Acquisition Support Center. He is a writer-editor for Network Runners Inc., with more than 30 years of editing experience at newspapers, including the McClatchy Washington Bureau, The Sacramento Bee, the San Jose Mercury News, the Dallas Morning News and the Fort Worth Star-Telegram. He holds a Bachelor of Journalism degree from the University of Missouri.

