
Defensive Cyber Operations pilots a new funding approach for software acquisition and development.
by Jennifer Sevier
For years, there has been a disconnect between modern software acquisition requirements and congressional funding sources. Software acquisition funding has traditionally been spread across three separate appropriations categories: Research, Development, Test and Evaluation (RDT&E); Other Procurement Army (OPA); and Operations and Maintenance Army (OMA). This diffused approach has posed acquisition challenges to organizations such as the Program Executive Office for Enterprise Information Systems’ Defensive Cyber Operations (DCO), whose mission is to rapidly deliver innovative and dominant cyberspace capabilities to the nation’s cyber defenders.
Until recently, the specific ways in which government programs like DCO were able to spend money hindered innovation. In fiscal year 2021, however, Congress initiated a new pilot project to bridge the gap between budgeting categories and software procurement. Through the pilot, DCO and other participants have been able to more efficiently progress through acquisition cycles and deliver critical capabilities to warfighters in a timely manner.

DIGITAL DEFENSE: A Soldier participates in a defensive cyber software testing exercise in September 2020, during Cyber Quest, an annual event at Fort Gordon, Georgia. (Photo by Jennifer Sevier, DCO)
CYBER SOFTWARE PROCUREMENT CHALLENGES
Project management has two primary methodologies: waterfall and agile. Current policies and regulations treat software acquisition as a waterfall—a series of steps and sequential phases. This approach is at odds with modern software development, since software is treated as a depreciating asset. Assets need to be continually updated with new functionality, upgrades, license renewals and cloud hosting environments, but current policies restrict the ability to interchange appropriations as new requirements emerge.
Due to the speed at which cyber threats evolve, and the fast pace of industry innovation in countering them, it is nearly impossible for Army cyber defenders to identify the software tools they will need one to two years in advance. Program managers often have only months or weeks in which to identify specific cyber defense tools for procurement. This short acquisition lead time poses difficulties when program managers are forced to either procure a new software system with OPA funds or renew existing licenses with OMA funds. Doing this creates unfunded requirements in the year of execution, and hinders program offices from adequately planning or acquiring appropriate tools and resources for critical software requirements.
Additionally, at any given time, software tools rapidly progress through multiple acquisition phases: prototyping, production and sustainment. Because of the highly dynamic and evolving cyber threat environment, programmers and financial managers cannot accurately forecast how much of each type of funding will be needed until the required year of execution.
In short, a modern approach is needed to align acquisition pathways with budget processes.
PILOTING A NEW APPROACH
As part of the fiscal year 2021 Presidential Budget Request, DOD announced a new multi-year pilot program to assist program managers in their responsiveness to warfighters’ needs. The Budget Activity 8 (BA-08) Software and Digital Technology Pilot is a testing solution which realigns existing funds—spanning multiple appropriations—into a single appropriation budget activity. It is important to note that the BA-08 pilot is not a new funding appropriation; it is housed as an additional budget activity under RDT&E. This activity is supportive of agile software acquisition and development, and aims to remove budgetary constraints for program managers.
Nine existing and fully funded military efforts were proposed for the fiscal year 2021 pilot program, and in the summer of 2020, DCO officially became the first and only Army organization chosen to participate. By consolidating software programs from all phases of the acquisition life cycle into the BA-08 pilot, DCO set out to improve funding and execution decisions, build more cohesive acquisition strategies and optimize program management support in the delivery of critical capabilities to cyber defenders. To track the pilot’s success, DCO and other pilot program participants are required to collect and report financial measures and performance metrics to the undersecretary of defense for acquisition and sustainment.
DCO is taking advantage of the BA-08 pilot in support of the DOD’s January 2020 modification of the Directive 5000 series, including the implementation of the Adaptive Acquisition Framework. This framework centers on rapid and continuous delivery of software capabilities, supporting DCO in its objective of delivering effective and affordable solutions to the cyber warfighter in a timely manner. Since the current budget process still operates independently and is not timely or flexible for short-notice or rapid software procurement, the BA-08 pilot provides a welcome solution.
DCO’s project manager, Col. Mark Taylor, has been a champion of the pilot program. “Using the BA-08 will optimize budgeting efforts, mitigate delays in software acquisition and reduce overall costs in procuring critical capabilities,” said Taylor. “It will also reshape our acquisition strategies to better support the timely delivery of our products and enable us to remain ahead on today’s cyber battlefield.”
TESTING TECH: During the September 2020 Cyber Quest exercise, cyber warriors participated in experiments to help Soldiers fight and defend against cyber attacks, prevent cyber threats and identify gaps in software technology. (Photo by Jennifer Sevier, DCO)
ACQUIRING CAPABILITY—FASTER
DCO procures and prototypes comprehensive cyberspace weapons systems for the Army. Prioritizing capabilities for cyber mission forces is critical to remaining ahead of today’s evolving cyber threats. It is incumbent upon DCO to ensure that data breaches and malicious activity do not happen on DOD Information Network. By the end of fiscal year 2021, the DCO team found that the use of the BA-08 pilot led to faster acquisition lead times for many of its mission-critical capabilities, including cloud hosting for research, testing and software procurement.
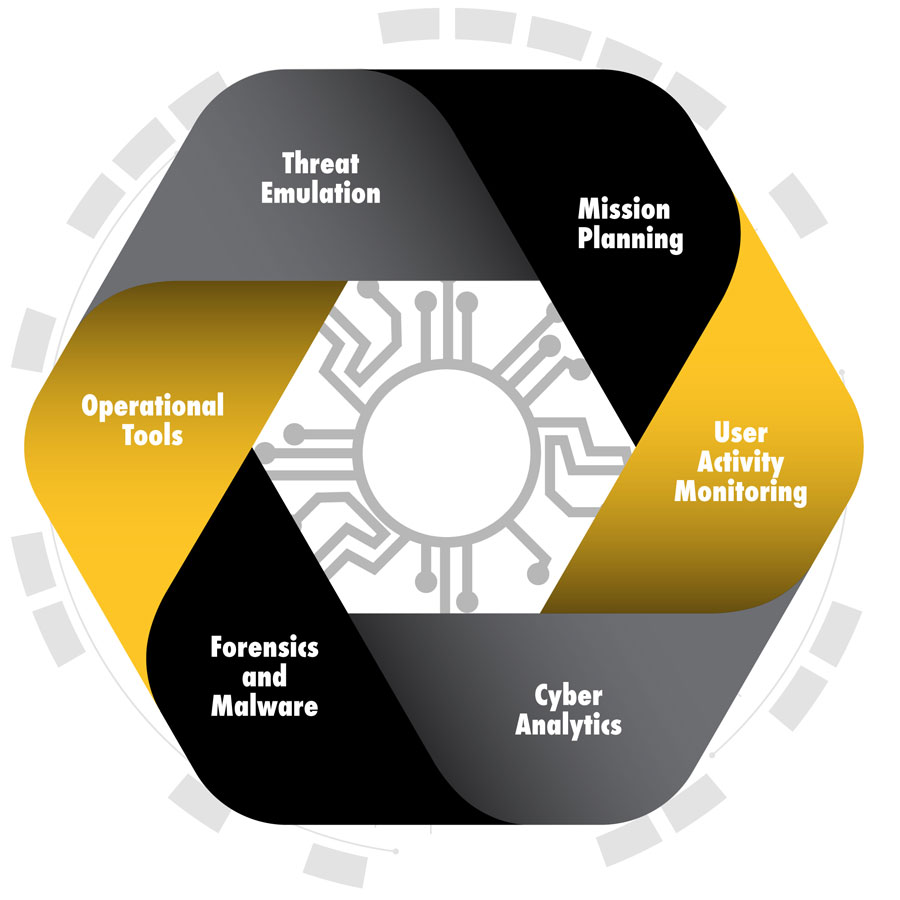
DEFENSIVE SUITE: Defensive Cyber Operations’ software tools are a full-spectrum solution developed to assess, deter, deny, defend, defeat and evolve against the insider threat. (Graphic by U.S. Army Acquisition Support Center and Jennifer Sevier, DCO)
SOFTWARE PROCUREMENT
There are several steps in procuring software—from identifying a need, to prototyping a solution, to testing the environment and determining the longevity of technologies and license agreements. Historically, the RTD&E appropriation focused on hardware systems that have longer lifespans than software. The BA-08 pilot is allowing DCO to be more responsive to the dexterous environment of software procurement and development.
DCO’s capabilities cover an array of threats and associated solutions, with each piece of software simultaneously integrating with the next. DCO’s software tools proactively identify cyberspace threats through simulation exercises and actively monitor current network activities—a full spectrum of solutions to assess, deter, deny, defend, defeat and evolve against insider threats.
DCO performs user testing before full deployment of all its systems, and has identified the need for continuous updates, licenses and integration. Soldiers use the systems in real-life scenarios and give feedback to test engineers. Recently, Soldier feedback and testing identified a system that was no longer effective in deterring cyberspace attacks. Based on operational needs, cyber defenders requested a new software tool that could be used to capture, index and correlate real-time network data.
Decommissioning the obsolete software would have required an above threshold reprogramming action from OMA to OPA, necessitating congressional approval. By using the BA-08, DCO was able to procure and provide user testing to cyber warfighters with a cost avoidance of over $3 million. Soldiers have been able to prototype and test new software with optimal results in a timely manner.
CLOUD HOSTING
Gabriel Nimbus is the Army’s big data platform. It provides analytics and visualization tools for large amounts of data collected by the DOD Information Network. These analytics facilitate counter-reconnaissance activities meant to discover the presence of cyber threats and vulnerabilities. The platform is also the Army’s number one defensive cyberspace operations weapons system, providing an integrated technology solution. These capabilities drive decisions, enhance situational understanding and promote automation, while enabling cyberspace warfighters to achieve their objectives.
In fiscal year 2021, the amount of data being aggregated and stored in the cloud exponentially increased due to escalating cyber threats. This unforeseen growth in data collection needed to be funded immediately. DCO tracks cloud hosting as an operational expense that is usually paid with OMA funds. Prior to the enactment of the fiscal year 2021 Defense Appropriations Act, DCO did not have access to flexible BA-08 authorities. If DCO had been able to use a single appropriation at the time, the organization could have reprioritized funds to better equip Gabriel Nimbus and immediately increase its storage capacity.
I fiscal year 2022, the BA-08 was fully in place, and DCO was able to address the storage capacity in rapid time, discovering the presence of advanced cyber threats and vulnerabilities on non-classified and classified networks.
“With the agile nature of the BA-08, DCO is able to quickly execute procurement and acquire cutting-edge technology for the cyber battlefield,” said Lt. Col. Dakota Steedsman, product manager for DCO’s Cyber Analytics and Detection. “Having the BA-08 funding line allows us to move forward with modernization while keeping our systems operational. Cloud hosting and license renewal are critical to our continuous modernization.”
CONCLUSION
The use of multiple types of funding has caused many of DCO’s portfolio acquisition challenges in procurement, agile software development, license renewals and technology modernization. The BA-08 pilot allows the project management office to rapidly integrate and revolutionize critical technologies for our cyber warfighters. DCO plans to use the BA-08 as a tool to responsively fund software procurement and development efforts in the rapidly evolving cyber domain.
Based on the fiscal year 2021 results of the pilot—which has been extended through fiscal year 2022—DCO is continuing to participate in the DOD’s BA-08 pilot. By the conclusion of the pilot, the optimal outcome for the defense acquisition community would be for Congress to establish a new single appropriations category for software and digital technology. This monumental step would ensure that program managers could prioritize and control how funding is spent on emerging technologies based on warfighter or other end-user needs, change mission profiles and other external drivers, and deliver innovative and cost-effective solutions.
“We are doing this work with the understanding that the next near-peer war will be won or lost in the cyber domain, well before the first Soldier touches down on the battlefield,” said Taylor. “Having a single appropriation dedicated for software-intensive acquisition ensures Army readiness in the defense of our networks.”
For more information, go to: https://www.eis.army.mil/programs/dco.
JENNIFER SEVIER provides strategic communication support to Defensive Cyber Operations at Fort Belvoir, Virginia, for Octo Consulting. She has 20 years of communication and marketing experience for public and private sector communities.

